A) Download the configuration
B) Run a credentialed scan.
C) Conduct the assessmenet during downtime
D) Change the routing to bypass the router.
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Management wishes to add another authentication factor in addition to fingerprints and passwords in order to have three-factor authentication. Which of the following would BEST satisfy this request?
A) Retinal scan
B) Passphrase
C) Token fob
D) Security question
F) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Ann, a user, reports she is unable to access an application from her desktop. A security analyst verifies Ann's access and checks the SIEM for any errors. The security analyst reviews the log file from Ann's system and notices the following output: 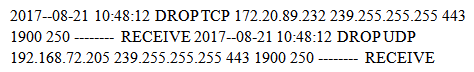 Which of the following is MOST likely preventing Ann from accessing the application from the desktop?
Which of the following is MOST likely preventing Ann from accessing the application from the desktop?
A) Web application firewall
B) DLP
C) Host-based firewall
D) UTM
E) Network-based firewall
G) B) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A hacker has a packet capture that contains: 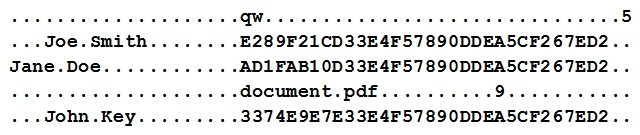 Which of the following tools will the hacker use against this type of capture?
Which of the following tools will the hacker use against this type of capture?
A) Password cracker
B) Vulnerability scanner
C) DLP scanner
D) Fuzzer
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A preventive control differs from a compensating control in that a preventive control is:
A) put in place to mitigate a weakness in a user control.
B) deployed to supplement an existing control that is EOL.
C) relied on to address gaps in the existing control structure.
D) designed to specifically mitigate a risk.
F) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Joe a computer forensic technician responds to an active compromise of a database server. Joe first collects information in memory, then collects network traffic and finally conducts an image of the hard drive. Which of the following procedures did Joe follow?
A) Order of volatility
B) Chain of custody
C) Recovery procedure
D) Incident isolation
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
After correctly configuring a new wireless enabled thermostat to control the temperature of the company's meeting room, Joe, a network administrator determines that the thermostat is not connecting to the internet-based control system. Joe verifies that the thermostat received the expected network parameters and it is associated with the AP. Additionally, the other wireless mobile devices connected to the same wireless network are functioning properly. The network administrator verified that the thermostat works when tested at his residence. Which of the following is the MOST likely reason the thermostat is not connecting to the internet?
A) The company implements a captive portal
B) The thermostat is using the incorrect encryption algorithm
C) the WPA2 shared likely is incorrect
D) The company's DHCP server scope is full
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A customer calls a technician and needs to remotely connect to a web server to change some code manually. The technician needs to configure the user's machine with protocols to connect to the Unix web server, which is behind a firewall. Which of the following protocols does the technician MOST likely need to configure?
A) SSH
B) SFTP
C) HTTPS
D) SNMP
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company offers SaaS, maintaining all customers' credentials and authenticating locally. Many large customers have requested the company offer some form of federation with their existing authentication infrastructures. Which of the following would allow customers to manage authentication and authorizations from within their existing organizations?
A) Implement SAML so the company's services may accept assertions from the customers' authentication servers.
B) Provide customers with a constrained interface to manage only their users' accounts in the company's active directory server.
C) Provide a system for customers to replicate their users' passwords from their authentication service to the company's.
D) Use SOAP calls to support authentication between the company's product and the customers' authentication servers.
F) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
In a lessons learned report, it is suspected that a well-organized, well-funded, and extremely sophisticated group of attackers may have been responsible for a breach at a nuclear facility. Which of the following describes the type of actors that may have been implicated?
A) Nation state
B) Hacktivist
C) Insider
D) Competitor
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which of the following is a security consideration for IoT devices?
A) IoT devices have built-in accounts that users rarely access.
B) IoT devices have less processing capabilities.
C) IoT devices are physically segmented from each other.
D) IoT devices have purpose-built applications.
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An application was recently compromised after some malformed data came in via web form. Which of the following would MOST likely have prevented this?
A) Input validation
B) Proxy server
C) Stress testing
D) Encoding
F) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A security analyst is investigating a potential breach. Upon gathering, documenting, and securing the evidence, which of the following actions is the NEXT step to minimize the business impact?
A) Launch an investigation to identify the attacking host
B) Initiate the incident response plan
C) Review lessons learned captured in the process
D) Remove malware and restore the system to normal operation
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A security analyst is interested in setting up an IDS to monitor the company network. The analyst has been told there can be no network downtime to implement the solution, but the IDS must capture all of the network traffic. Which of the following should be used for the IDS implementation?
A) Network tap
B) Honeypot
C) Aggregation
D) Port mirror
F) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
When connected to a secure WAP, which of the following encryption technologies is MOST likely to be configured when connecting to WPA2-PSK?
A) DES
B) AES
C) MD5
D) WEP
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A security analyst is determining the point of compromise after a company was hacked. The analyst checks the server logs and sees that a user account was logged in at night, and several large compressed files were exfiltrated. The analyst then discovers the user last logged in four years ago and was terminated. Which of the following should the security analyst recommend to prevent this type of attack in the future? (Choose two.)
A) Review and update the firewall settings
B) Restrict the compromised user account
C) Disable all user accounts that are not logged in to for 180 days
D) Enable a login banner prohibiting unauthorized use
E) Perform an audit of all company user accounts
F) Create a honeypot to catch the hacker
H) D) and E)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A security administrator has completed a monthly review of DNS server query logs. The administrator notices continuous name resolution attempts from a large number of internal hosts to a single Internet addressable domain name. The security administrator then correlated those logs with the establishment of persistent TCP connections out to this domain. The connections seem to be carrying on the order of kilobytes of data per week. Which of the following is the MOST likely explanation for this company?
A) An attacker is exfiltrating large amounts of proprietary company data.
B) Employees are playing multiplayer computer games.
C) A worm is attempting to spread to other hosts via SMB exploits.
D) Internal hosts have become members of a botnet.
F) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A technician is implementing 802.1X with dynamic VLAN assignment based on a user Active Directory group membership. Which of the following configurations supports the VLAN definitions?
A) RADIUS attribute
B) SAML tag
C) LDAP path
D) Shibboleth IdP
F) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which of the following is a component of multifactor authentication?
A) RADIUS
B) SSO
C) Transitive trust
D) OTP
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
During certain vulnerability scanning scenarios, it is possible for the target system to react in unexpected ways. This type of scenario is MOST commonly known as:
A) intrusive testing
B) a buffer overflow
C) a race condition
D) active reconnaissance
F) None of the above
Correct Answer

verified
Correct Answer
verified
Showing 421 - 440 of 1164
Related Exams